Hi everyone,
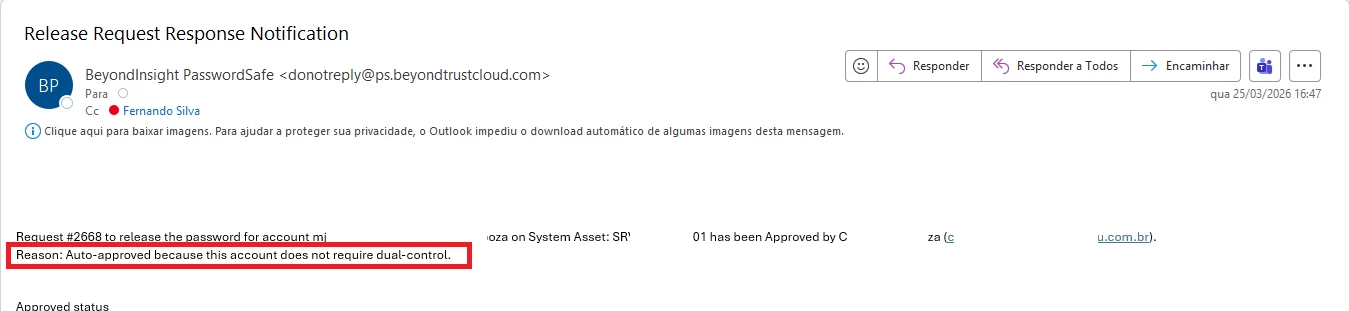
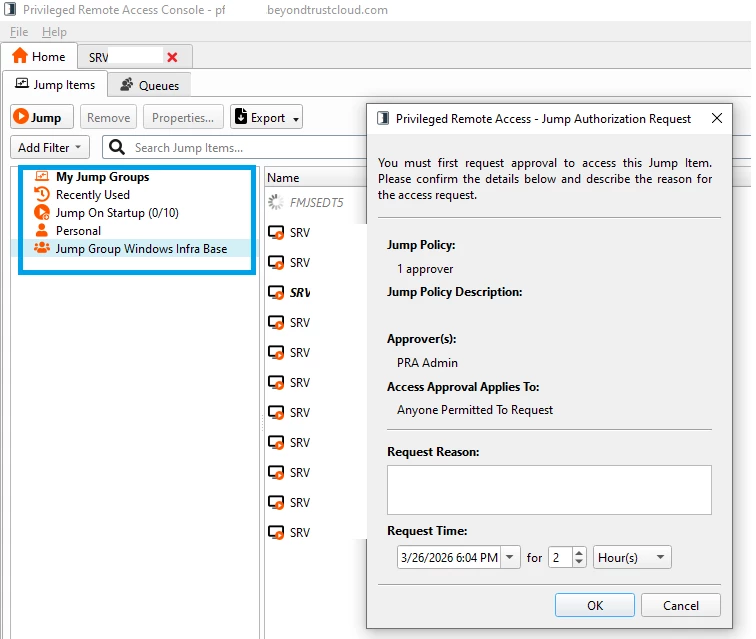
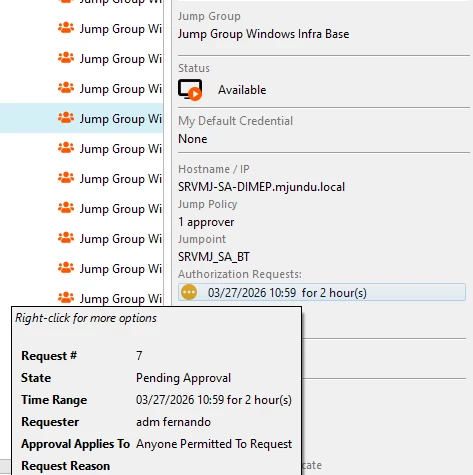
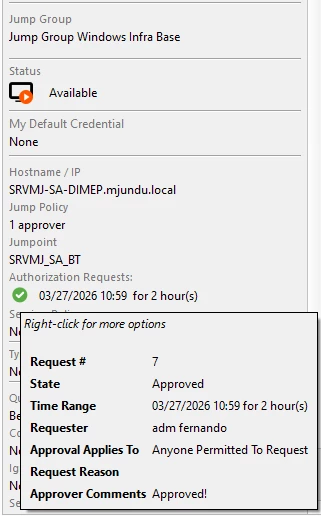
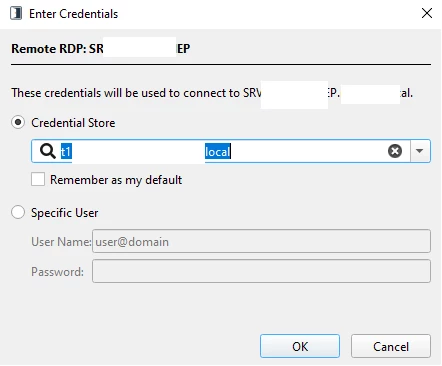
I have a question regarding PASM. I have users and devices managed through Password Safe, and session delivery is handled by PRA. If I want a user connecting from PRA with credentials injected from Password Safe to provide a reason for connecting, where do I configure this in PS or PRA? Also, if they need an approval workflow, where do I configure that in PS or PRA?