Hello,
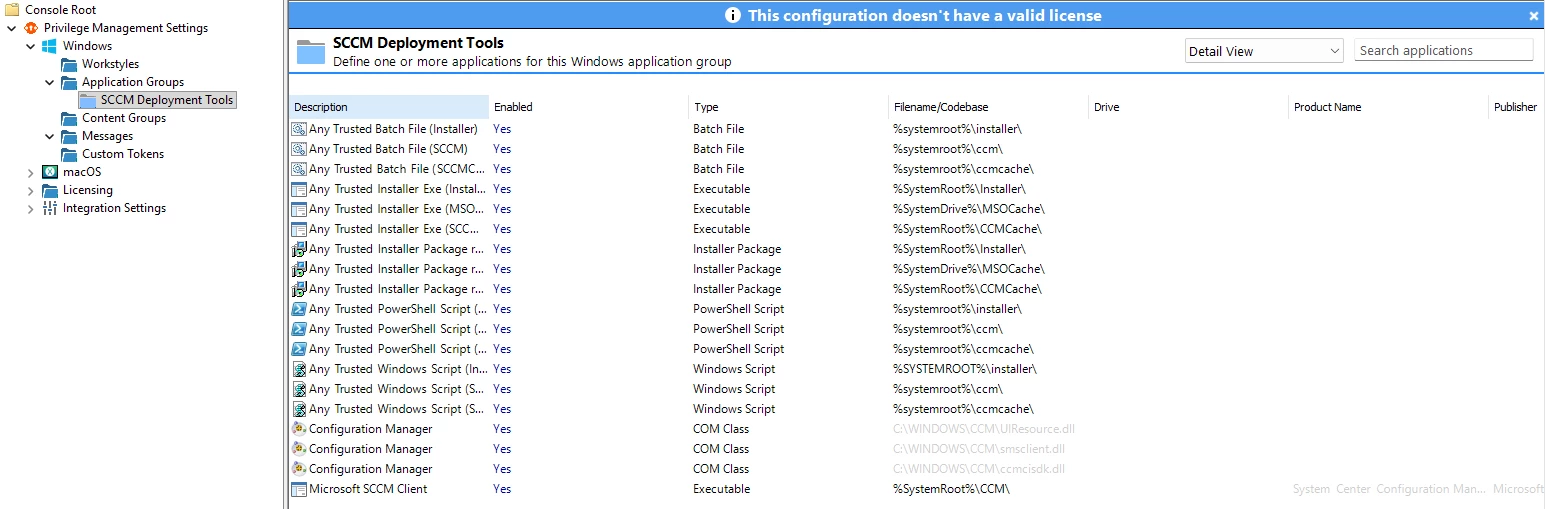
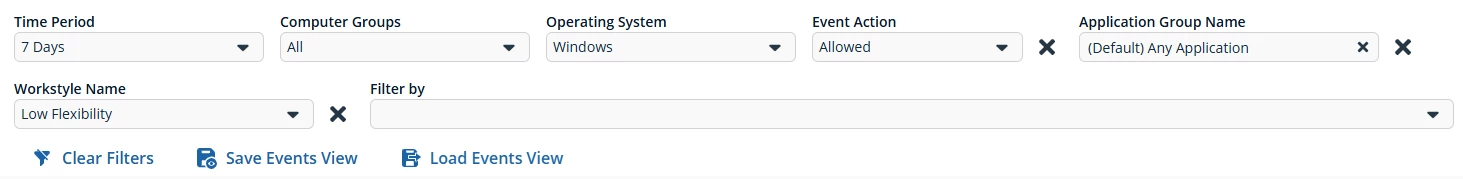
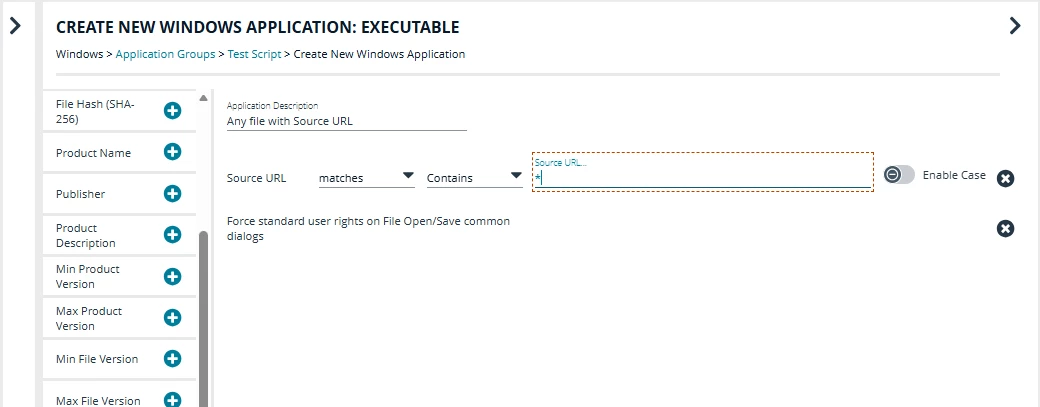
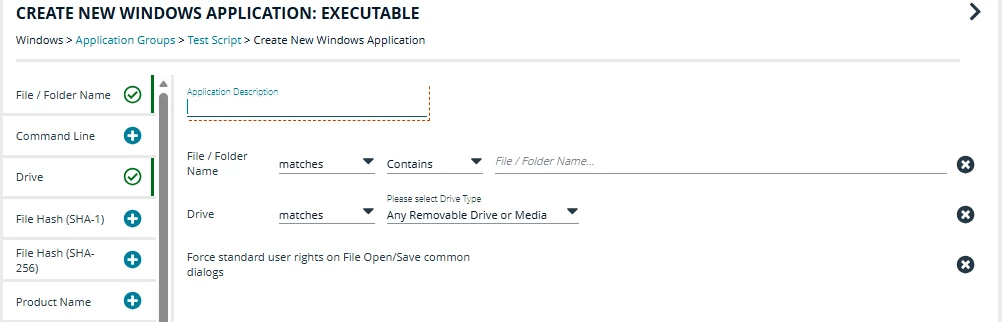
I am working on creating a new BT EPM policy for our Win 10 and 11 system in our environment. I created an application group and added it under Low Flex workstyle. I am trying to create a policy that will block all the applications except the ones i have approved in SCCM Software Center and InTune. My problem is that i have a list of couple of hundred of approved apps and i don’t want to add them in the application group manually one by one.
is there a way to import them from an excel list if i populate the excel with publisher and product name and whatever else i might need. or is there any API i can use for that.
Thank You